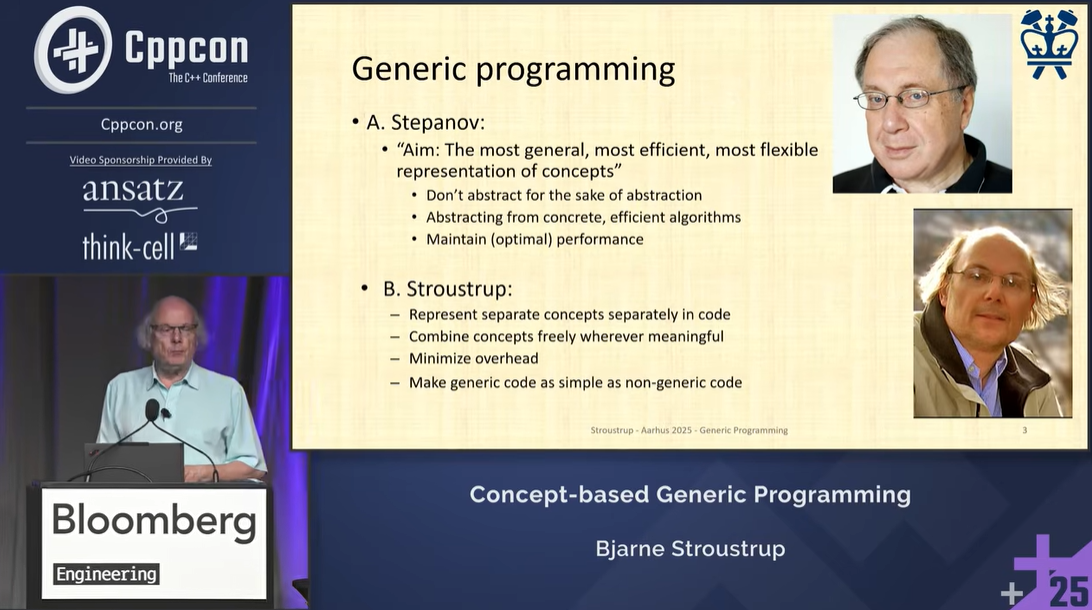
CppCon 2025 Concept-based Generic Programming -- Bjarne Stroustrup
 Registration is now open for CppCon 2026! The conference starts on September 12 and will be held in person in Aurora, CO. To whet your appetite for this year’s conference, we’re posting videos of some of the top-rated talks from last year's conference. Here’s another CppCon talk video we hope you will enjoy – and why not register today for CppCon 2026!
Registration is now open for CppCon 2026! The conference starts on September 12 and will be held in person in Aurora, CO. To whet your appetite for this year’s conference, we’re posting videos of some of the top-rated talks from last year's conference. Here’s another CppCon talk video we hope you will enjoy – and why not register today for CppCon 2026!
Concept-based Generic Programming
by Bjarne Stroustrup
Summary of the talk:
This talk presents programming techniques to illustrate the facilities and principles of C++ generic programming using concepts. Concepts are C++’s way to express constraints on generic code. As an initial example, it provides a simple type system that eliminate narrowing conversions and provides range checking.
Concepts are used throughout to provide user-defined extensions to the type system. The aim is to show their utility and the fundamental ideas behind them, rather than to provide a detailed or complete explanation of C++’s language support for generic programming or the extensive support provided by the standard library.
The final sections briefly present design rationales and origins for key parts of the concept design, including use patterns, the relationship to Object-Oriented Programming, value arguments, syntax, concept type-matching, and definition checking. They also mention static reflection, a C++26 improvements in the support of general programming.

 In today's post, I will explain one of C++'s biggest pitfalls:
In today's post, I will explain one of C++'s biggest pitfalls:  Even experienced C++ developers sometimes stumble on a deceptively simple question: what actually happens when a destructor throws an exception? This post breaks down the mechanics behind stack unwinding,
Even experienced C++ developers sometimes stumble on a deceptively simple question: what actually happens when a destructor throws an exception? This post breaks down the mechanics behind stack unwinding, 
 Registration is now open for CppCon 2026! The conference starts on September 12 and will be held
Registration is now open for CppCon 2026! The conference starts on September 12 and will be held  Registration is now open for CppCon 2026! The conference starts on September 12 and will be held
Registration is now open for CppCon 2026! The conference starts on September 12 and will be held  Registration is now open for CppCon 2026! The conference starts on September 12 and will be held
Registration is now open for CppCon 2026! The conference starts on September 12 and will be held