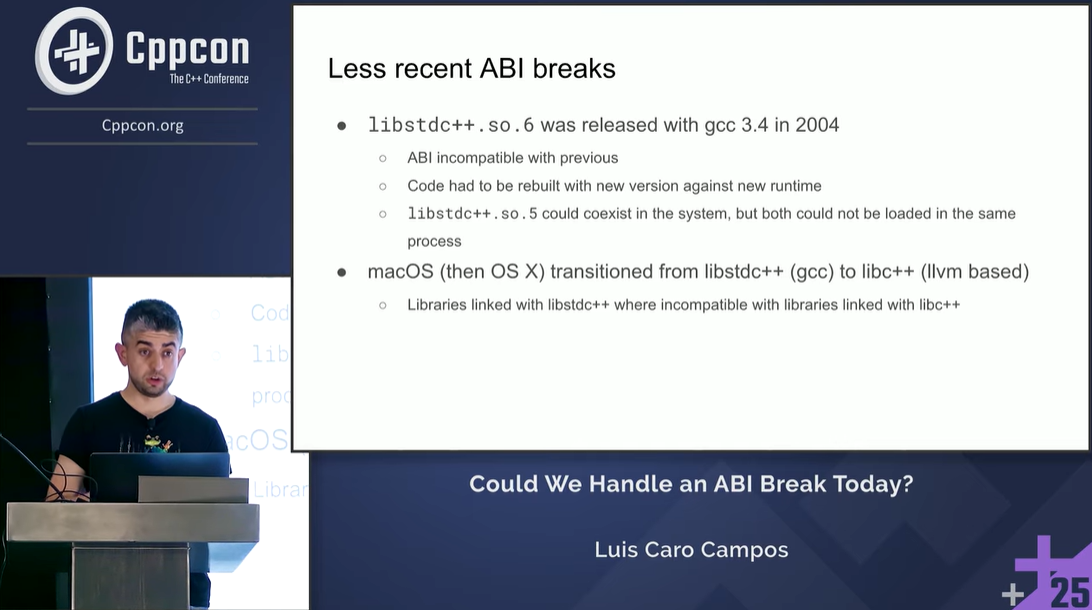
CppCon 2025 Could C++ Developers Handle an ABI Break Today? -- Luis Caro Campos
 Registration is now open for CppCon 2026! The conference starts on September 12 and will be held in person in Aurora, CO. To whet your appetite for this year’s conference, we’re posting videos of some of the top-rated talks from last year's conference. Here’s another CppCon talk video we hope you will enjoy – and why not register today for CppCon 2026!
Registration is now open for CppCon 2026! The conference starts on September 12 and will be held in person in Aurora, CO. To whet your appetite for this year’s conference, we’re posting videos of some of the top-rated talks from last year's conference. Here’s another CppCon talk video we hope you will enjoy – and why not register today for CppCon 2026!
Could C++ Developers Handle an ABI Break Today?
by Luis Caro Campos
Summary of the talk:
The C++ Evolution Working Group recently reaffirmed its commitment to ABI stability, prioritizing link compatibility with C and older C++. The C++11 libstdc++ ABI updates introduced in gcc 5.1, although not strictly “breaking”, are still in the collective memory of C++ developers and this experience shows us how sensitive the ecosystem is to ABI updates.
This talk challenges the assumption that a future ABI break would be equally problematic, as the landscape has evolved significantly in the last decade.
On the one hand, the C++ standard has evolved in such a way that even if the standards committee and compiler vendors go through great lengths to avoid breaking the ABI of standard library implementations, library authors are not as cautious - so in practice, the ability to link objects built with different C++ standard levels does not hold true for a lot of cases.
On the other hand, tooling has evolved significantly in this time period. For example, both Conan and vcpkg are able to “tag” binaries on some arbitrary ABI version. We can see similar examples in other tools or ecosystems that need to work around ABI complexities.
This talk is not intended to argue about the merits or risks of future ABI changes - but to ask ourselves the question: are we overestimating the pain of a future ABI break?

 Mixing your units can be disastrous. Wu Yongwei takes a quick look at C++ unit libraries that can help keep everything in order.
Mixing your units can be disastrous. Wu Yongwei takes a quick look at C++ unit libraries that can help keep everything in order. Registration is now open for CppCon 2026! The conference starts on September 12 and will be held
Registration is now open for CppCon 2026! The conference starts on September 12 and will be held  Registration is now open for CppCon 2026! The conference starts on September 12 and will be held
Registration is now open for CppCon 2026! The conference starts on September 12 and will be held  In today's post, I will explain one of C++'s biggest pitfalls:
In today's post, I will explain one of C++'s biggest pitfalls: