Adding State to the Update Notification Pattern, Part 1 -- Raymond Chen
 In software development, handling notifications efficiently is pivotal, particularly in user interface scenarios. While traditional notification patterns inform handlers of changes, they often lack crucial state information. In this article, we explore the intricacies of managing stateful updates within the context of C++/WinRT, addressing challenges such as race conditions and ensuring that notification handlers operate on the most recent data for optimal user experience.
In software development, handling notifications efficiently is pivotal, particularly in user interface scenarios. While traditional notification patterns inform handlers of changes, they often lack crucial state information. In this article, we explore the intricacies of managing stateful updates within the context of C++/WinRT, addressing challenges such as race conditions and ensuring that notification handlers operate on the most recent data for optimal user experience.
Adding State to the Update Notification Pattern, Part 1
by Raymond Chen
From the article:
Some time ago, we looked at the update notification pattern, but in those cases, the notification carried no state.
Consider the case where you want to call a notification handler, and the handler also receives a copy of data derived from the most recent state, rather than just being called to be told that something changed and forcing them to figure out what changed.
For example, suppose you want to add autocomplete to an edit control, but calculating the autocomplete results is potentially slow, so you want to do it in the background. But while you are calculating the autocomplete results, the user might type into the edit control, and you want the final autocomplete results to reflect the most recent edit in the edit control, rather than any results from what the edit control used to contain at some point in the past.

 In this episode, you learn how default parameters work and why you shouldn't put them on virtual member functions.
In this episode, you learn how default parameters work and why you shouldn't put them on virtual member functions. The last episode of the series about SObjectizer and message passing:
The last episode of the series about SObjectizer and message passing: During the last two weeks, we saw a bug related to uninitialized values and undefined behaviour, we listed the different kinds of initializations in C++ and we started to more detailed discovery with copy-initialization. This week, we continue this discovery with direct-, list- and aggregate-initialization.
During the last two weeks, we saw a bug related to uninitialized values and undefined behaviour, we listed the different kinds of initializations in C++ and we started to more detailed discovery with copy-initialization. This week, we continue this discovery with direct-, list- and aggregate-initialization.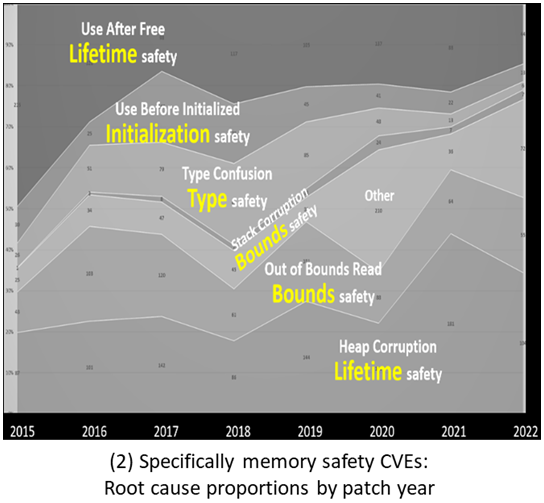 The safety of C++ has become a hot topic recently. Herb Sutter discusses the language’s current problems and potential solutions.
The safety of C++ has become a hot topic recently. Herb Sutter discusses the language’s current problems and potential solutions. A new episode of the series about SObjectizer and message passing:
A new episode of the series about SObjectizer and message passing: